Ocarina of Time. Here’s the story of how some fans made it happen anyway, all on a stock N64 with a cartridge Ocarina unmodified.” title=”How Zelda fans changed the ending to Ocarina of Time on a vanilla N64 4″ data-lazy-src=”https://cdn.arstechnica.net/wp-content/uploads/2022 /07/triforce-percent-sgdq-800×605.png”/><img src="https://cdn.arstechnica.net/wp-content/uploads/2022/07/triforce-percent-sgdq-800×605.png" alt="Ceci… n’est pas censé se produire dans Ocarina of Time. Here’s the story of how some fans made it happen anyway, all on a stock N64 with a cartridge Ocarina unmodified.” title=”How Zelda fans changed the ending to Ocarina of Time on a vanilla N64 4″/> Summer games done quickly
Shortly following our quick finish summer games guide 2022 went live, the event hosted an amazing demo of a classic video game — a demo that has since cluttered responses to this Ars article. If we want to cut hair, it crosses the classic N64 from 1998 Legend of Zelda: Ocarina of Time is not a “speedrun”, but it is another example of the “TASBot“concept transforming games in ways we never dreamed of 24 years ago.
archyde news
The team of fans and programmers responsible for this week’s “Triforce-percent” demo have since revealed how they achieved the feat with nothing more than a stock N64 and an original Ocarina retail cartridge, though the secret involves controller inputs so fast and precise they can’t be done by anything less than a computer.
Nothing stale in this race
A video from early 2020 that explains how stale reference manipulation works. You may want to watch this before watching the SGDQ 2022 video, embedded below.
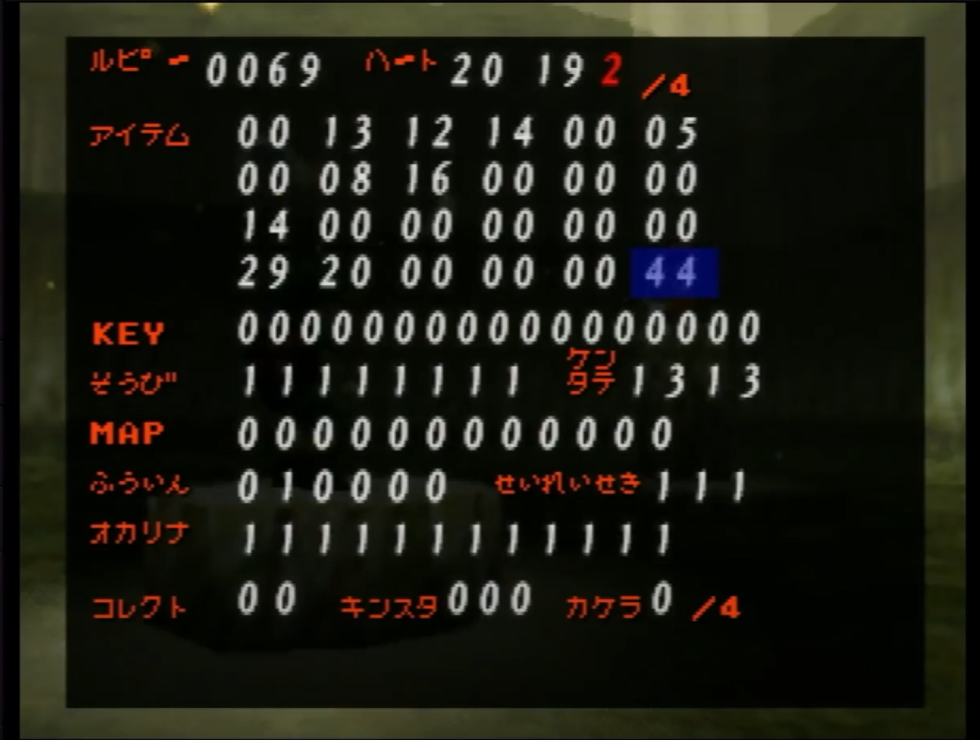
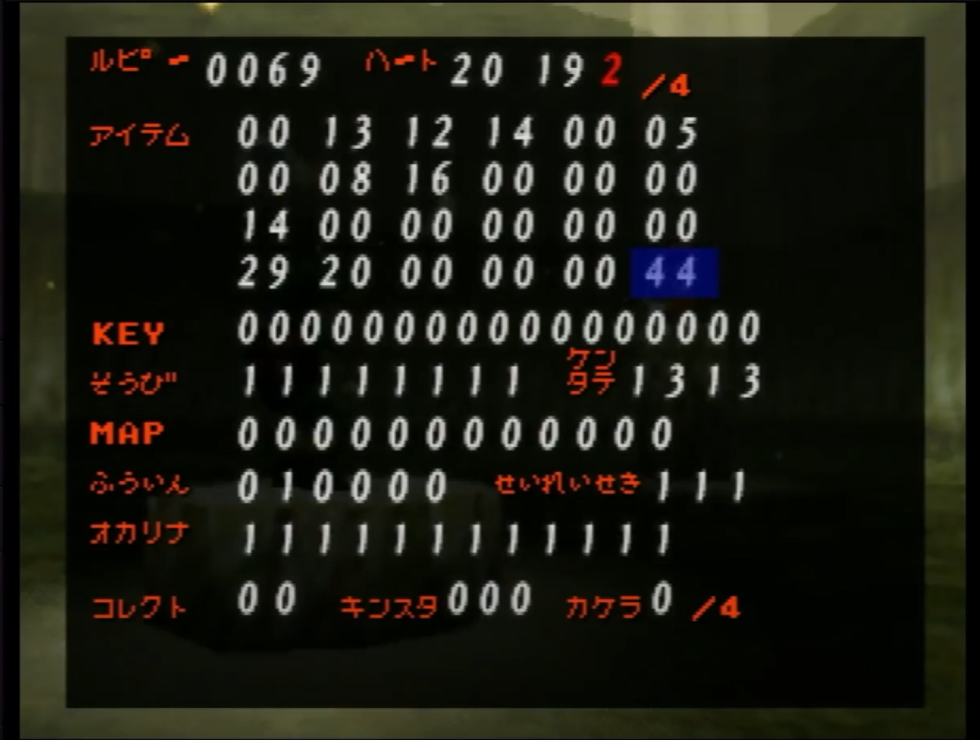
The 53-minute demo (embedded at the end of this article) opens with an exploit previously unearthed in late 2019, which the community has dubbed “Outdated reference manipulation.” This exploit takes advantage of a vulnerability in the original 1.0 version of the game, which allowed players to manipulate numerical values assigned to specific objects in the game’s memory. The most airy explanation of this complicated technique can be found in a YouTube video from early 2020 (embedded above), as it spells out the various numerical values assigned to each object in the game, such as their X, Y, and Z axes and rotation.
Savvy gamers can make the values overlap or overwhelm the original game code so they can be manipulated as they see fit. The technique we see in this week’s run requires Link to pick up a rock while traversing a “loading zone”, a hallway used to hide loading breaks on N64 gear, and do so in a way that the game was not designed to handle.
Initially, this exploit was a speedrunning tool, as it might trick the game into loading the final credits sequence and technically count as a “completion” in just a few minutes. But the Triforce-percent race goes much deeper.
INTEGRATE new content into a classic game
Summer games done quickly
By picking up and dropping specific objects, then making the game’s hero Link move and performing maneuvers in a specific sequence, the TASBot team opens a Pandora’s box of so-called arbitrary code execution. , the type of vulnerability used by hackers around the world to trick a closed computer system into executing whatever code they want. Additionally, the TASBot motion and command chain begins telling the N64 to accept button input from all four N64 controllers as if it were code.
Summer games done quickly
At this point, a computer takes over all four ports of the N64 controller and sends out a rapid series of clicks, like it’s a zillion-fingered superhero equivalent to The Flash. The glitched out Ocarina instructed the N64 to accept each button press in a way that matches specific code strings. Once enough of that payload has been sent, the team can resume normal control over the “player one” port, so a real person can play through a whole new sequence of content, all being dumped into the N64’s random access memory (RAM) by the incredibly fast input of the other three controllers.
These on-the-fly patches can do a lot of amazing things that, combined, look like a fully blown patch of a cartridge’s ROM, though the TASBot team is limiting itself to changes that apply specifically to the Console RAM: Tiny changes to existing code, total file replacements, or commands to tell the game to ignore content it would normally load from ROM. As a result, this exploit may glitch or crash if players stray from the expected path this exploit is optimized for.



